Venmo is a very popular mobile app which simplifies payments among friends. Once you link your bank account or credit card, you can start sending money to others, instantly.
With Venmo, you are not limited to just make payments. It allows you to charge others as well. Say your friend had no cash for that tasty burrito and you paid for it. You have the option to be proactive and “charge” your friend using Venmo. Charging someone does not mean that the money will be withdraw from his account, it just means that he will get a notification and see the pending payment in his account. Your friend has to accept the charge in order for the payment to happen. And this functionality is what we are going to take advantage of.
Venmo notifications
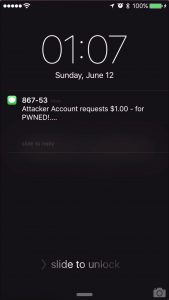
Just as any other mobile app, Venmo has a notification system to keep you up to date with any charges, payments, etc. By default, notifications are processed and rendered by the app. Every time something relevant happens, you will see the familiar alert pop-up on your mobile device screen.
Some time ago, a friend charged me for a bottle of Gin he bought while we were 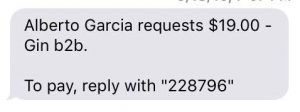 partying at Bay2Breakers. I hate invasive notifications so I have them all disabled. However, instead of the classic “App notification”, I got an SMS. I’ve never notice this before and immediately thought this was a new feature in Venmo. Looking at the it, I realized that it was not just a notification, it was a call to action. The SMS gave me the option to reply with a 6-digit code in order to make the payment. I did so, and as expected the payment was processed.
partying at Bay2Breakers. I hate invasive notifications so I have them all disabled. However, instead of the classic “App notification”, I got an SMS. I’ve never notice this before and immediately thought this was a new feature in Venmo. Looking at the it, I realized that it was not just a notification, it was a call to action. The SMS gave me the option to reply with a 6-digit code in order to make the payment. I did so, and as expected the payment was processed.
This had me thinking I hadn’t authenticated to Venmo in order to make the payment. I simply replied to a text with the code I was given and that seemed sketchy.
Stealing money from locked devices
As mentioned above, one of the things you can do with Venmo is send a payment request to someone. It is as simple as paying somebody but instead of clicking “pay”, you click “charge”. The weekly limit is $2,999.99, hence the title of this post.
I remembered that you can use Siri to send SMS when your device is locked. It is worth noting that this feature is on by default and became especially popular when the “Hey Siri” feature was added in iOS 9.
Now that we know we can send SMS on locked devices, we need the code present in the SMS in order to reply and make the payment. Apple introduced the “Text Message Preview” which allows you too see in the lock screen who sent you a text and part of the content. This is also on by default.
If we combine these two, I am able to see the SMS with the code and can reply using Siri. All this without unlocking the device. All this out of the box. WIN?!?
Venmo’s SMS notification
Once I reproduced the attack on my phone, I was very excited. But before running to report it to Venmo, I wanted to make sure it was working on other devices. I tested on my girlfriend’s iPhone and to my surprise, I did not get an SMS. This ruined everything as in order for this attack to be “significant” I was looking to make it happen on devices with default configurations. Yes, I could see texts on the lock screen. Yes, I could reply to texts using Siri. But Venmo’s SMS notification was not enabled by default. I must have enabled it at some point in the past.
I really wanted to make this possible under default settings so I looked at everything all over again. While checking the SMS service, I started to reply with random characters which resulted in another SMS reply like the one below:
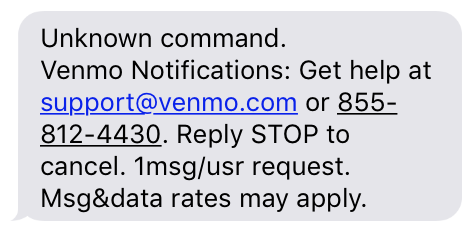
When I read the SMS again I realized that I did not pay attention to the most important part: “Reply STOP to cancel”. Hmmm… If I can reply STOP to cancel the SMS notification service, can I send a text with the word START and activate it?
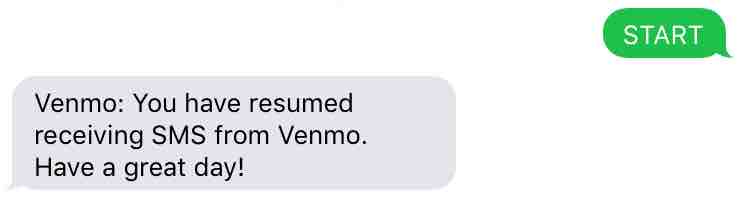
BINGO! You can activate the SMS notification service by sending an SMS to 86753 with the word “Start”. 86753 is a short code number owned by Venmo and used for all the SMS notifications.
Now, I am able to activate Venmo’s SMS notification service, see the secret code and reply to make the payment. All that without unlocking the device!
Venmo’s patch and workaround
When I reported this to Venmo, together with the other findings you can read below, they decided to fix this particular issue by adding additional spaces to the SMS that contains the 6 digit code. Because the Text Preview feature only shows a limited number of characters, Venmo added enough spaces to the SMS to prevent the code from been displayed on the lock screen preview.
Unfortunately, this fix is not good enough. I found a really easy workaround in which I could still find out the code. Again, all I had to do was to use Siri to “Read my latest text”. While I could not read it myself anymore in the lock screen, I can have Siri read it for me. Simple and effective!
Demo
Preventing this attack
There are several issues here and to be honest, this is not all Venmo’s fault. The problem is not just that you can pay by replying to an SMS. The problem is also that you can see the text and reply to it without unlocking the device. That is on Apple.
Venmo also let’s you enable the service over SMS and that should not be possible. Venmo should remove that functionality which will prevent this attack entirely (unless you already have it enabled). Given that disabling Venmo’s SMS notifications is not effective, you should disable SMS preview. You can also disable Siri in the lock screen so no one can send texts on your behalf.
Other possible attacks
Now that we know how to abuse the SMS notification system to make money, I wanted to further explore the possibilities of this service. After all, we still need physical access to the mobile device in order to perform this attack. I wanted to see if I could do the same thing but without having to see the SMS, basically brute-forcing the code.
I charged my own account to receive the SMS and started to input incorrect codes. I was expecting to have a number of tries and have the payment be canceled but instead, I got an SMS informing me that I exceeded the number of tries and that I would have to wait a bit to try again. Interesting! The payment is not canceled, there is simply a time based protection in place to make brute-forcing more difficult.
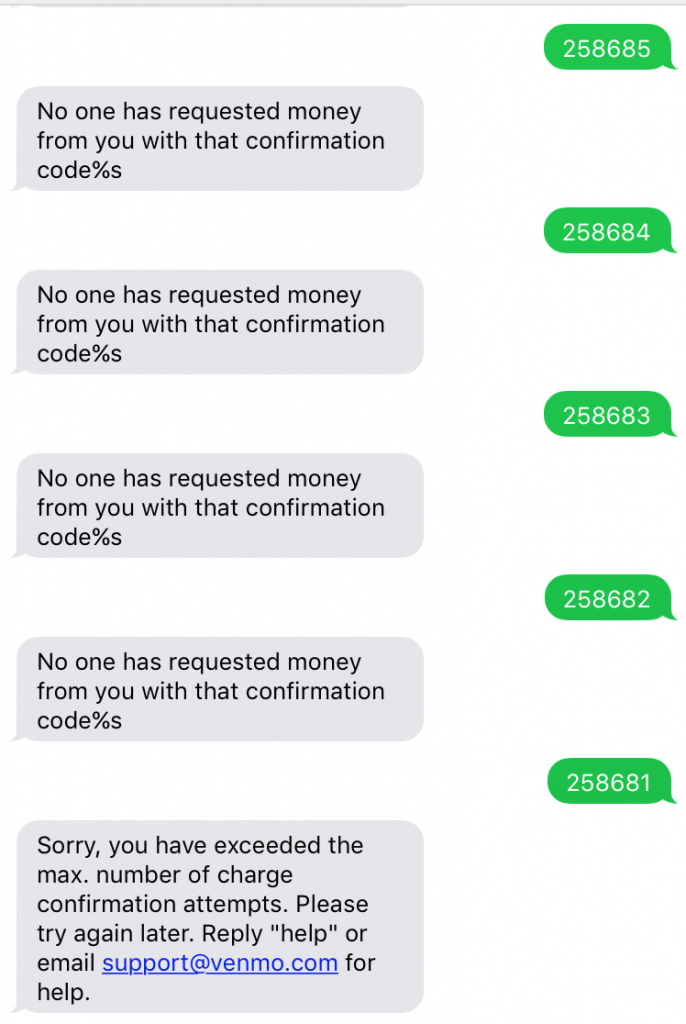
Have you noticed it too? “No one has requested money from you with that confirmation code %s“. Venmo told me there was no security impact, just a typo.
Anyway, the point is, after 5 tries I had to wait about 5 minutes till I could try another 5 times. The codes are six digits long so we have 1 million possibilities and we can try 5 codes every 5 minutes. Do the math. Possible but not feasible.
Codes are linked to payment requests
Since we cannot brute-force the entire code space, I tried to send 2 charge requests instead of one. Basically, I wanted to see if once I send the second charge request, the first one will be invalidated together with the code. Turns out that is not the case. Every charge request is associated to a new code without invalidating previous requests. This means that instead of sending one request and brute-forcing a million codes, I can send multiple charge requests and reduce the number of codes I have to guess!
I used Burp to look at the API and indeed, I was able to send 50 payment requests in a matter of seconds. Of course, this is very noisy. Remember that the victim will get one notification for every charge request… We need to improve this.
One request to multiple victims
My previous approach was to send multiple requests to the same victim in order to reduce the number of codes I have to guess. Since that is too noisy, I can send only one request but to multiple people instead.
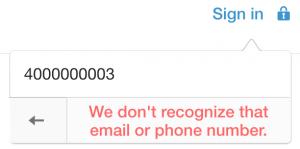
User enumeration makes finding victims very simple and it takes just a few lines of code to write a script that will return a million valid Venmo user emails/phone numbers.
Instead of sending a million requests to one victim, we send one request to a million Venmo users. Once we do this, all we have to do is send a text to Venmo’s service with the same code for all the million users. Statistically we should at least have one match. We cannot forget about having to spoof the phone number of the victim when sending the SMS. That is trivially easy with services like Twilio though.
These attacks are theoretical and I did not try them. Venmo payments are known to be monitored and the last thing I want is someone knocking at my door asking why so many people owes me money.
Again, when I reported this to Venmo, they responded that it was not possible because of three reasons:
Short Code numbers cannot be spoofed
Venmo told me that it should not be possible to spoof SMS messages to short codes since they bypass SMS gateways where the spoofing would need to occur. I did not find how to do it either. Because this prevents the attack entirely, I started thinking that a short code number must be associated to a real number. And if I find the real number, I could perform the attack as I explained above because I would be able to spoof the sender.
Doing some tests with the settings in Venmo’s web, I managed to get a text from +1(646)-679-6604 instead of the shortcode 86753. Awesome! I also confirmed that you can get the charge notification through the shortcode number but reply with the 6 digit code to the real number. The payment will still happen making the attack possible again.
rate limiting MAKES user enumeration too expensive
Venmo thinks that it is not possible to enumerate accounts massively since “there is rate limiting in place to prevent abuse of this endpoint“. The problem here is that this is an unauthenticated call (you try to recover the password because you cannot log in) which means, the only way to have rate limits is to check from which IP the multiple requests are coming from. We can easily bypass this protection by using a list of proxies and iterate over them. Our IP will change every few requests without much performance impact (we need max 1 million valid accounts). Venmo should simply return the same message whether the phone number is valid or not.
Daily rate limit to the number of charge requests
Venmo claims that a user can only do a limited number of charge requests per day and that “it would prevent this attack scenario from scaling to the point where it would significantly improve your chances for brute forcing”.
In reality, this makes the attack more tedious rather than impossible. The charge request limits are applied at a per user basis. It is possible to create multiple Venmo accounts and switch between them every time the request limit is reached. My tests indicate that you can make up to 50 charge requests per day. On average, you would need ~1500 accounts to successfully perform this attack. You also need a valid phone number to create an account which makes it trickier.
Responsible disclosure
As I mentioned, I disclosed my findings to Venmo responsibly. They accepted some of the issues I found, proposed patches and mentioned that some of my assumptions were incorrect. I explained above some of the workarounds I found already and I shared that with Venmo as well.
After some back and forth, Venmo took following steps to secure the app:
- They killed the SMS “reply-to-pay” functionality. There was no good way to fix it. I am glad Venmo decided to kill a feature VS keeping it knowing it has flaws.
- The real number cannot be used anymore. You cannot receive an SMS from the shortcode number and reply to the real number now.
- The %s typo in the SMS was fixed
Communication with Venmo’s security team was smooth and professional. They kept me updated on the fixes as those were pushed to production and generally it was a good experience.
Timeline
- June 1st, 2016: Disclosure to Venmo
- June 8th, 2016: Venmo acknowledges some issues and discards others
- June 10th, 2016: I question some patches and assumptions made by Venmo
- June 15th, 2016: Venmo agrees and decides to kill the “reply-to-pay” feature
- July 18th, 2016: Venmo notifies me that all fixes have been deployed

This was interesting, thanks for sharing!
Thank you for reading it!
Does this still work? Can you teach me?
does it work
and how so?
Very interesting, great work and loved the way you “showed you work” allowing me to get a better handle on how security professionals can problem solve.
Also, the best news is they learned to disable authenticating payments through SMS. The only part of your article I disagreed with was the assumption that it’d be best if SMS preview and reply was turned off from the lock screen.
A) there are a number of life saving scenarios where being able to read and reply to texts without requiring an unlock. These include situations where the phone owner falls unconscious or is otherwise disabled as well as situations where important info needs to be shared when the person is driving, etc.
B) texts are extremely easy to get sent to another device or to snoop on in other ways. Remember that it was recently decided that SMS can no longer be used for authentication for this very reason.
C) the feature “hey Siri” makes the iPhone usable for millions of people who do not have use of their hands. It is important that we do not allow people who are disabled to be inherently less secure because “oh well, they should’ve disabled the feature”.
Which is why fundamentally, no exchange of money should ever be confirmed via text.
It is the responsibility of developers to ensure the information they send over SMS is not used to authenticate or do other information critical exchanges. In fact, doing so is quickly becoming illegal.
Thanks for reading and providing feedback! I was maybe misleading but I did not meant to say that the solution was to disable Siri in lock screen. I said that while Venmo does not fix the issues, disabling Siri is an alternative solution. While you are right that Siri is super useful when the device is locked, this is still insecure and in my opinion you should have the option to enable it, but it should be off by default.
Specifically to your points, I would say that:
A) In life threatening situations you call 911 which is available even without Siri
B) That’s true, but just because there are other ways to do it, that should not be a reason to not start somewhere to fix it.
C) Agree 100%. That is why I mentioned that it should be an option to enable it but it should be secure by default.
Thanks again for the feedback!
Hey need to talk to you about this how is that possible ? Please
Email
Hey Boss Teach Me How Can I Do This Am From Malawi Please
Indeed, just send me an email
Can u do that for em bro
Can u do that for em bro if u can thats my email Toshka.abdo@yahoo.com
How does it really work
bro teach me I need money asap
does this still work?
How does this work plz im a single dad, and I need $800 to get a car today. My son’s bday is today, and I need food for us…plz help me
Can you tell me how to do this
Interested
Nice work man. I’m surprised they didn’t offer any sort of bug bounty for this.
Thanks! Yeah, unfortunately Venmo does not have a public bug bounty
I’m not a security guy per se but that was a very interesting read. Thanks for writing it up.
Thanks! Glad you liked reading it!
Can you bypass blackchain
Can you help me please…. Im from SA
Great job!! now go work on saving the rest of the world
Hehehe, you got it! :)
I would like to know what software is that in the lighting bolt. Thanks. http://imgur.com/a/O6kZ9
It’s Monosnap. Very handy for screen recording and free. https://monosnap.com
Nice Information Dude, Thanks
awesome stuff buddy,
i hate these companies who think there code and dev teams are the best,
don’t get me wrong i wouldnt know where to start on systems like that but there getting paid for there ability lol,
i like your approach and your tactics,
and your motives for these “attacks” is for the better good of everyone and ethical
and the way you wrote it up makes it crystal clear and a good read
companies need to relise we are about 100 years behind in regards to security when it comes to the protection of the electronic data, so no matter what they make someone or some group of people will find a way as i’m sure you’ve proven that point more then once lol
and when the prize is money like the above write up it gives the unethical persons enough reason to find that way to win the prize
when is money safe?
when its in your hand not in a server
My business account was hacked using Venmo & I don’t even subscribe to their service! I am in the middle of dealing with getting repayment of my monies from my bank…written to State Attorney Generals office, Consumer Financial Protection, Better Business Bureau….any other suggestions? My thoughts are go to local & national TV stations to try to make other people aware of this!!!
That’s strange! If you don’t have a Venmo account link to your bank account, how did they manage to gain access through Venmo? Could you provide more details if possible? It is a very interesting case. Feel free to send me an email
That is the million dollar question! I do NOT use Venmo! In my correspondence with my bank, they (customer service reps) said they didn’t even know what or who Venmo was. I discovered the money missing on January 16, 2017 and went down to the bank on 17th. The monies were taken on November 9th from my business account….the statement said” Mastermoney purchase, POS purchase terminal 12345678 Venmo 085581244 NY”. The bank seems to think they used my debit card. I chatted online with Venmo and they gave me the name (first name & last initial) of the person that received the money but would not give me any other info because of their “privacy laws”. The bank has not told me exactly what they are doing or whether my money will be refunded but will advise me by April 17, 2017.
I have contacted OCC, BBB, State Attorney General’s office & Consumer Financial Credit Bureau. Most responses have asked if I am satisfied with bank’s response …obviously I am not satisfied.
So, if I understand correctly, someone stole your debit card info and added it to their Venmo account to later make a purchase? That is pretty crazy, first time I hear that story. Thanks for sharing it with us. I hope everything will be fine on your side and you get a refund!
This does not look like a Venmo security issue – or is it?
First someone appears to have used your account credentials on a fake Venmo account.
Second – how did Venmo validate this bank account belonged to the fake Venmo account. This is the problem that needs to be worked on for all online payments.
Why do you have to talk to these tech companies so many times before they understand the flaws in their applications I don’t particularly use this Money Transfer app but I do use one. I also see you looking for a website I’m not sure what that means
About 2 weeks ago, I reported a basic loss of functionality to Venmo through their customer support. Issue not fixed and when I followed up for anticipated resolution today (4/3/17), the CSR wouldn’t/couldn’t tell me if the issue I reported two weeks ago was in their support database. Hmmmmm.
ISSUE: Loss of copy functionality on iPhone (there still is copy functionality in the desktop version; not sure about Android) when attempting to copy historical information from a transaction. When holding my finger down, the copy balloon does not activate. This loss of functionality began when some changes to the UI were rolled out by Venmo about 2-3 weeks ago. When initially reporting this loss of functionality to Venmo (3/20/17), they denied this functionality was missing even after I asked them to attempt replicating on a support person’s iPhone. Hmmmm. Then I reached out to 5 random users of Venmo in Atlanta and each one of them confirmed they did not have this functionality either. I reported this to Venmo Support on 3/22/17. A trouble ticket was generated by Yelena in CS on same date.
I’ve worked for Siebel, Oracle, and SaaS startups and worked with my Support teams to resolve client issues. I’d have to give Venmo low marks for their responsiveness and expertise regarding follow up, documenting issues (the CSR I spoke with on 4/3/17, said the issue I described to Yelena on 3/22/17 was not documented in their support system; she asked me to describe the issue again), and resolving them.
It’s a very good app but their resolution of a basic functionality issue on what is probably their largest installed base of users (iPhone users), leave me wanting. Thoughts?
Hello,I read your blogs named “How to steal $2,999.99 in less than 2 minutes with Venmo and Siri – Martin Vigo” like every week.Your humoristic style is awesome, keep doing what you’re doing! And you can look our website about proxy list.
Dope blog. Keep it up!
HW CAN I GET IN TOURCH WITH U
hi this osamede agho i need $900.00 dollars delivered streate to my doore at my mailing address throught the usps mail. please
Did you use google voice to say it
Do it for me
Good morning
This item is not availablein my pakistan please any salution download app
Hi..its about vemo….
U mean the person snd me money by replying with the ode sent to him or her
I need paint we need a new couch until have a new living we need a new house
You realize this could never work in reality. The person will later log in to that phone to see where the money was sent. That’s tied to a bank account, which means all your real personal information will be tied to it, and you’re in jail before you can do this more than once or twice.
There are ways to prevent what you mention but this is not a guide on how to steal money from other people. This is an article about computer security and Venmo. Stealing is a crime and not cool.
i like what u are doing for enlighting world .keep it on can u show me the way out of poverity .Please i ned $10.000 to sponsor my music career.Am up coming artiste i from nigeria.Tanx
$750 taken from my account yesterday. Not a member of Venmo. Customer service person, “Alexandra” uses privacy policy like a shield to repel requests for help and information. She won’t even forward my concerns to Venmo fraud department, stating they only work with banks once a fraud complaint is issued.
do it right now plz
HI VIGO YOU CAN HELP ME TO STEAL MONEY TRUE MY PHONE
just what is the easy way to steal money by venmo??
i need this money to help my family and friends and inlaws
teach me man i need money
Is this really existed, or just a trick to fool people. ?
TEACH ME PLZ
pls teach me sir alexgojedan@gmail.com I will pay back
I love money
Kindly enlight me more on venmo
I want you people to help me make money fast because am from a poor country and from a poor family .
I want to make money in order to take care of my family as well as my self.
Please
Out of curiosity, wouldn’t this be a way around the Venmo not sending SMS to a VoIP? I have a VoIP cell provider and Venmo told me it won’t work. I texted start to that short code number after reading this and got a reply back: “Venmo: You have resumed receiving SMS from Venmo. Have a great day!” Venmo said I couldn’t sign up because I was incompatible with their SMS system. If I’ve signed up to receive their SMS, and it is functioning, shouldn’t I then be able to register my number and be able to get an account?
Just a thought for a way for Venmo to work around the loss of all the VoIP users out there. But I doubt they would listen to an uncredentialed problem solver like me. ;-)
What if I open a new bank account today and close it the day after I get the money? Or the day I get the money
How do you kick the problem of getting the amount that venmo sends to the bank for verification to add a bank account
I’m just an older, ‘joe blow’ user of anything with today’s tech. As a lot of us older gen, my sons have taught me a lot the years to help keep me safe.
THANK YOU for explaining everything so a laymen can understand it!
It’s like algebra for me! I understand all the concepts, & in my own head can figure general things out, BUT TO WORK OUT A PROBLEM….FORGET ABOUT UR! 🙄😬
THANK AGAIN! Gratefully for the SECURITY DUDES LIKE YOU OUT THERE!
You are smart.
Tell me about this I want to know more
Couldn’t you still ask Siri to read the message, even when the phone is locked?